
How Firehorse Architecture Reduces Traditional Vendor Risk
Introduction
As a businessperson, all the machinery related to data security and privacy may seem inscrutable. It basically comes down to this: you trust your data to another company (the data processor) which then entrusts it to another set of companies (sub-processors) and everyone checks a box that states they will practice best standards.
Enterprise procurement and IT teams have to be rigorous.
Over the past two decades, vendor risk has grown more complex. Multi-tenant SaaS platforms, global data flows, sprawling sub-processor networks, and centralized data lakes have created real exposure. Encryption standards, access controls, sub-processor disclosures, and audit certifications are not bureaucratic exercises; they are rational responses to architectural realities.
At Firehorse, we take those concerns seriously. But we also believe something important and fundamental has changed.
Because of how we are architected, many traditional vendor security questions are no longer risk drivers in the same way they were for legacy SaaS providers. Not because they are unimportant, but because the underlying model has shifted.
This post explains that shift.
The “Chef in Your Kitchen” Analogy
One way to conceptualize the Firehorse model is simple:
Firehorse Agents are like sending a chef to your kitchen.
The chef:
Uses your ingredients
Cooks with your equipment
Operates within your house rules
Leaves everything in your kitchen
They do not take your ingredients out of the home.
They do not cook in a central facility.
They do not mix your ingredients with another customer’s.
They do not send your ingredients to another chef.
Technically, this means:
Our container runs in your cloud account.
Your encryption keys protect stored data.
Your monitoring stack captures activity.
Your networking policies control outbound calls.
Your compliance framework governs the environment.
Firehorse provides intelligence and automation capability, without assuming custody.
The Evolution of Enterprise Software Architecture
To understand why architecture matters, it helps to look at the progression of enterprise IT systems.
2000s: Most enterprise software was on-premise. Customers hosted and controlled everything. Vendor access was limited. Risk was primarily internal. Salesforce was one of the first big SaaS IPOs, in June 2004, a major milestone in the eventual shift from on-premise to SaaS as the dominant software delivery model. AWS launched in 2006.
2010s: Multi-tenant SaaS became dominant. Vendors hosted centralized environments. Customer data lived in shared infrastructure. The convenience was transformative, but so was the risk profile. Vendors now had custody of data. The vast majority of apps born in this era are “CRUD” apps (Create, Read, Update, Delete) with “WORM” data (Write Once, Read Many) stored in a database.
2024: Cloud-native 2.0 and AI-native systems emerge that no longer require centralized data custody to deliver value. Cloud maturity, containerization, and zero-trust design patterns make a different model possible.
Firehorse was built in this third era.
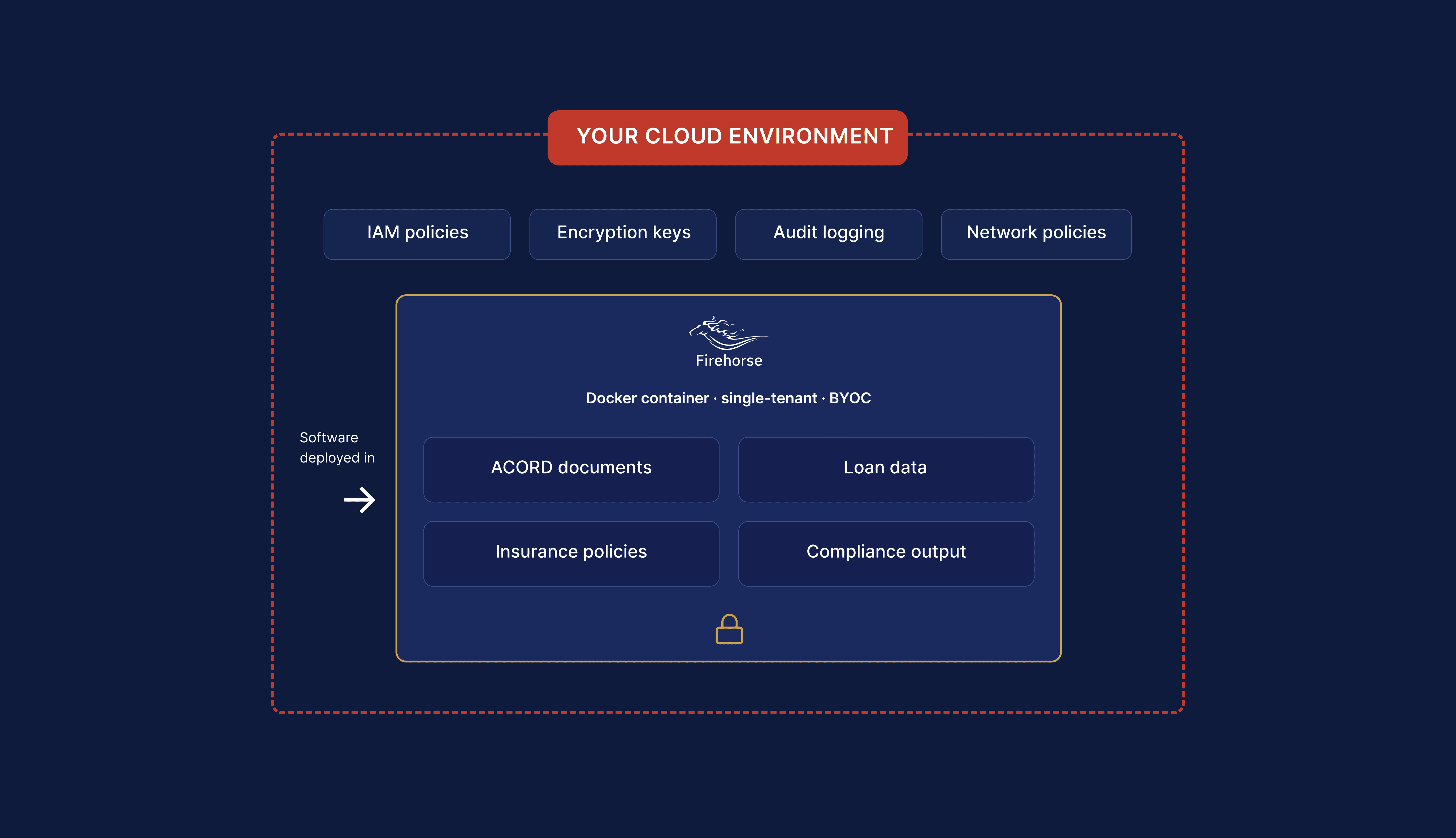
Firehorse Is BYOC and Single-Tenant by Design
Firehorse operates on a Bring Your Own Cloud (BYOC) model.
In practical terms, that means:
Firehorse software is deployed inside your cloud environment.
It runs as a Docker container within your infrastructure.
Your IAM policies govern access.
Your encryption policies apply.
Your logging and monitoring tools observe activity.
Your cloud security posture remains the controlling framework.
Client data never resides on Firehorse servers. We do not operate a centralized Firehorse data lake. We do not aggregate customer information across accounts.
Instead, our software operates where your data already lives.
This distinction is fundamental.
Traditional SaaS vendors take possession of customer data and then work to protect it. Firehorse does not take possession of your data in the first place. That architectural decision changes the risk surface significantly.
Security Posture Is Downstream of Architecture
Procurement and IT teams typically ask:
How is data encrypted at rest?
How is data encrypted in transit?
Who are your sub-processors?
Where is data stored geographically?
How is multi-tenant isolation enforced?
How do you prevent cross-customer exposure?
These are important questions in a centralized SaaS model because the vendor hosts, stores, and processes customer data in shared environments.
In a BYOC, single-tenant model, the answers look different:
Data at rest encryption is governed by your cloud configuration.
Data in transit encryption is enforced by your network policies.
With Firehorse, AWS Bedrock is the one external service involved, and it operates within the client's AWS environment. AWS guarantees no storage or logging of prompts.
Data residency is determined by your cloud region selection.
There is no cross-customer data exposure risk because environments are not shared.
The risk categories don’t disappear — they move under your control.
This is one of the core benefits of the model.
Zero-Trust by Design
Modern enterprise security frameworks emphasize zero-trust principles: never assume trust based on network location, vendor relationship, or implicit access.
Firehorse aligns with this philosophy at the architectural level.
You do not have to trust Firehorse with custody of your data because we do not possess it nor centralize it. Our employees do not access your production datasets. There is no Firehorse-managed multi-tenant environment where customer information accumulates.
Instead:
Access is governed by your identity systems.
Privileges are defined within your IAM framework.
Observability and audit logging live inside your monitoring stack.
This reduces counterparty risk.
In traditional SaaS, vendor compromise can create systemic exposure. In a BYOC model, each deployment is isolated within the client’s own cloud boundary.
Multi-Tenant vs. Single-Tenant: Risk Surface Comparison
Multi-tenant SaaS has delivered enormous efficiency to the enterprise. But shared infrastructure inherently creates shared risk surfaces:
Centralized databases
Cross-customer logical isolation controls
Vendor-managed encryption keys
Shared networking layers
Vendor-controlled patching timelines
By contrast, Firehorse is single-tenant native.
Each client environment is:
Isolated
Independently deployed
Governed by that client’s security policies
Free from cross-customer data paths
There is no shared passenger model. No shared storage layer. No shared data plane.
The isolation is structural, not procedural.
One Private External Processor
In centralized SaaS, sub-processor management becomes a major area of scrutiny. Vendors often rely on multiple downstream providers for hosting, storage, analytics, logging, support, and AI services.
Each sub-processor expands the data flow diagram.
In Firehorse’s architecture:
There is no third-party data storage processor.
There is no Firehorse-managed hosting layer.
There are no subcontractors accessing client data.
Where external services are used (for example, model inference), calls are executed from within your environment under your network policies and controls.
The result is a dramatically simplified vendor risk profile.
AI-Native Without Legacy Path Dependency
Many established SaaS providers are constrained by architectural decisions made 10–20 years ago. Centralized databases, monolithic stacks, and add-on compliance layers are difficult to unwind. Even if they attempt to add AI/ML features on top, they are still hamstrung by their legacy tech stack.
Firehorse was built recently, in a cloud-mature environment, with containerization and zero-trust assumptions from day one. We are not an AI wrapper. We are not a CRUD SaaS app.
This enables:
Stateless service design
Environment-agnostic deployment
Clean separation between software capability and data custody
Modular, updatable components
Generative user interfaces
There is no legacy data lake to protect.
There is no multi-tenant database to segment.
There is no inherited path dependency.
That flexibility allows us to align tightly with modern enterprise cloud standards.
What Actually Matters in This Model
Because architecture shifts risk, procurement conversations should focus on the right areas.
For Firehorse, meaningful diligence includes:
Container hardening practices
Software supply chain integrity
Image signing and verification
Role-based access control configuration
Outbound network policy definitions
Model call governance
Logging and audit integration
Patch and version management process
Secure SDLC practices
These are the controls that matter when software operates inside your cloud boundary.
We welcome those discussions.
Why This Model Justifies the Investment
Firehorse is not priced as a lightweight add-on tool. It is infrastructure deployed inside your environment, designed to automate critical workflows without expanding your external risk exposure.
The value proposition includes:
Operational automation of complex back-office processes, resulting in significant time and cost savings every month.
AI capability without centralized custody risk.
Alignment with enterprise cloud standards.
Reduced vendor exposure surface compared to traditional SaaS.
Elimination of cross-customer data commingling risk.
For enterprises that operate under strict compliance, regulatory, and internal audit requirements, reducing counterparty data risk is not a marginal benefit — it is foundational.
In many cases, the architectural alignment itself removes friction from security review cycles and vendor onboarding.
The Safest Place for Your Data
Enterprise IT teams invest heavily in securing their cloud environments:
Encryption key management
Network segmentation
Identity governance
Monitoring and alerting
Compliance certifications
Access reviews
Firehorse does not ask you to move your data outside that boundary.
The safest place for your data is often where it already lives — within the controls and guardrails your organization has spent years building.
Firehorse was designed to operate there.
Conclusion
Encryption, access controls, and compliance certifications remain critical in enterprise systems. We respect that. But architecture determines who holds risk.
By operating as a BYOC, single-tenant, containerized deployment within your cloud environment, Firehorse reduces the traditional vendor custody model that drives many SaaS risk concerns.
We do not centralize your data.
We do not aggregate customer environments.
We do not rely on downstream processors to host it.
We deliver intelligence and automation capability inside your existing security perimeter.
For procurement and IT leaders evaluating AI vendors, the question is not simply whether a vendor encrypts your data.
It is whether the vendor ever needs to hold it at all.
Firehorse was built so the answer is no.

Copyright © 2026 | Firehorse Group LLC

